

Cache Miss Attack
By Rajesh krishnakumar — “Go above and beyond!”
In today’s era, we all know what the advantage of caching systems are. Like how the cache is helping us speed up a process or request. But it has some downside too… Let’s discuss that today.
When the attacker purposely tries to cache miss, the attacker can overload your application and database.
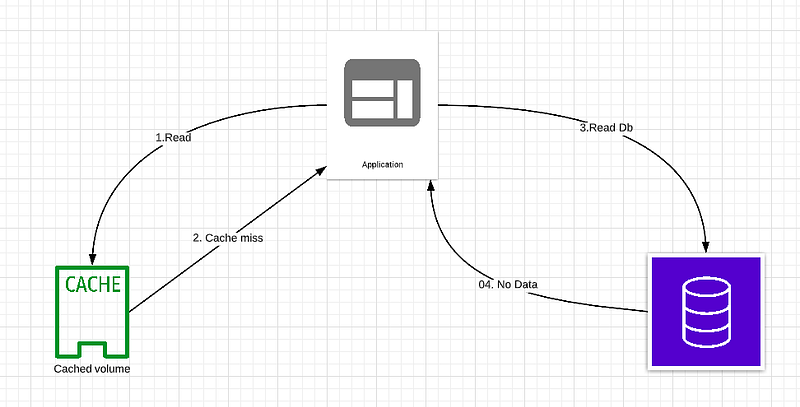
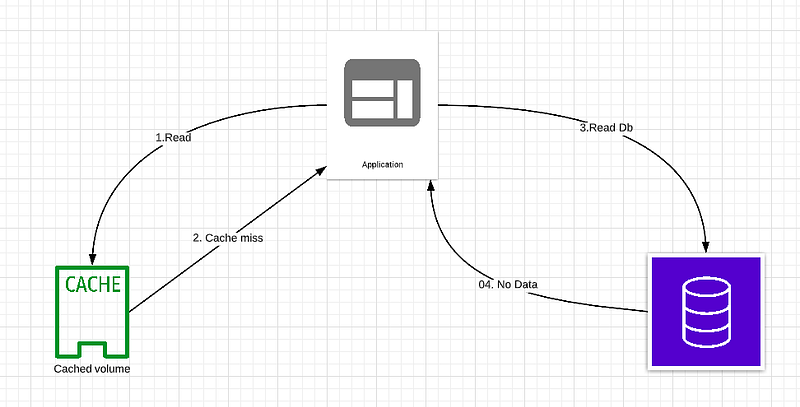
The below diagram just shows how a cache attack can take place
When a webpage is served from a cache

When a webpage is served from an application

So what happened in the above example, Let deep dive in.
When I hit example.com it served from the cache it took 60ms with response header x-cache: HIT
When I hit the same site with example.com?cachemiss it served from the application layer which took 3 sec with response header x-cache: MISS
This means the second request went to the application level and the database read.
If I give load like below mentioned. The application will be receiving an overwhelming request and eventually, the application will go down
Example.com?cachemiss1
Example.com?cachemiss2
Example.com?cachemiss3
We can strip all the parameters from the URL or keep the allowed parameter so we avoid cache miss-hit
For example:
This URL Example.com?cachemiss1 to Example.com or if this request came Example.com?cachemiss1 still it will search for Example.com in cache because cachemiss1 is not an allowed parameter
Use the cache effectively and reduce the Latency. Happy Caching!
Author
Rajesh krishnakumar
Editor
Mridula Saravanan
We at CaratLane are solving some of the most intriguing challenges to make our mark in the relatively uncharted omnichannel jewellery industry. If you are interested in tackling such obstacles, feel free to drop your updated resume/CV to careers@caratlane.com!
Leave a Reply